2020-02-25
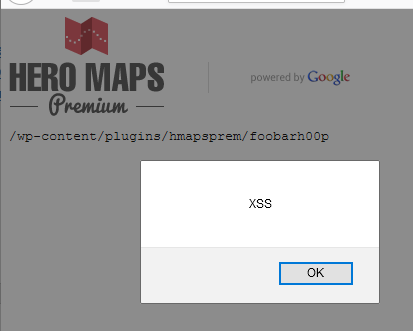
The Hero Maps Premium plugin for WordPress was prone to multiple cross-site scripting vulnerabilities because it did not sufficiently sanitize user-supplied input. An attacker may leverage this issue to execute arbitrary JavaScript in the browser of an unsuspecting user in the context of the affected site. This may allow the attacker to steal cookie-based authentication credentials or launch other attacks. The issues were corrected and a patch was made available (v.2.2.3).
Download Link: Hero Maps Premium
Vulnerable versions: v.2.2.1 and prior.
Googledork: 'inurl:/wp-content/plugins/hmapsprem'
Multiple reflected XSS vulnerabilities were identified in publicly-exposed endpoints of WordPress sites loaded with the Hero Maps Premium plugin. In each case, the application accepted input as HTTP parameters, which it later returned within the page as HTML or JavaScript. Multiple pages and parameters were susceptible to this attack.
The Hero Maps developer's professionalism and willingness to fix the issues were second to none. Upon notification, they worked to fully resolve the XSS issues and protect the Hero Maps users.
Hooper Labs takes security issues seriously. We believe in working with relevant stakeholders to achieve coordinated disclosure within a reasonable period of time. We also adhere to the industry-standard 90-day disclosure deadline, where vendors are notified of vulnerabilities immediately, with details shared to the public after 90 days (or sooner if the issues are resolved earlier).
Common Vulnerabilities and Exposures (CVEs) are an industry standard for identifying vulnerabilities (link). This system is a method for reference and tracking of publicly-known exposures. A CVE is a way to uniquely reference vulnerabilities across systems and Mitre Corporation is the primary CVE Numbering Authority (CNA) for the program. We believe that users have a right to know their exposures in order to make informed risk decisions.
Hooper Labs does not participate in bug bounty programs, but instead relies on responsible disclosure (link). Effectively communicating vulnerabilities and risks to the vendor, users, and public ensure that risk can be documented, calculated, and mitigated. We hope that through this process the Information Domain may be marginally safer.